Insight | Published 12 Apr 2026
CSCRF Is Changing the Compliance Conversation: What SEBI-Regulated Entities Should Prepare For
By Legal Research team
Tags: cscrf, sebi cyber resilience, cybersecurity compliance, cyber governance, cyber controls, audit readiness, operational resilience, sebi regulated entities, compliance operations, regtech
For a long time, many firms treated cyber as a specialist issue.
It sat with IT. Or information security. Or an outside consultant. Compliance might hear about it during audits, major incidents, or policy reviews, but it often did not sit at the center of day-to-day regulatory thinking. SEBI’s Cybersecurity and Cyber Resilience Framework, or CSCRF, pushes that conversation into a different place. The framework was issued on August 20, 2024 for SEBI-regulated entities, and SEBI followed it with clarifications on December 31, 2024. That sequence alone tells you this is not a side topic. It is now part of the operating expectations around regulated businesses.
The most important thing to understand is that CSCRF is not just about buying better security tools. SEBI says the framework aims to strengthen cyber resilience and maintain robust cybersecurity for regulated entities, and it supersedes earlier SEBI cybersecurity instructions listed in the framework. That is a broad signal. It means cyber is being treated as a structured control environment, not a loose collection of technical measures.
So what should firms prepare for?
The first theme is governance.
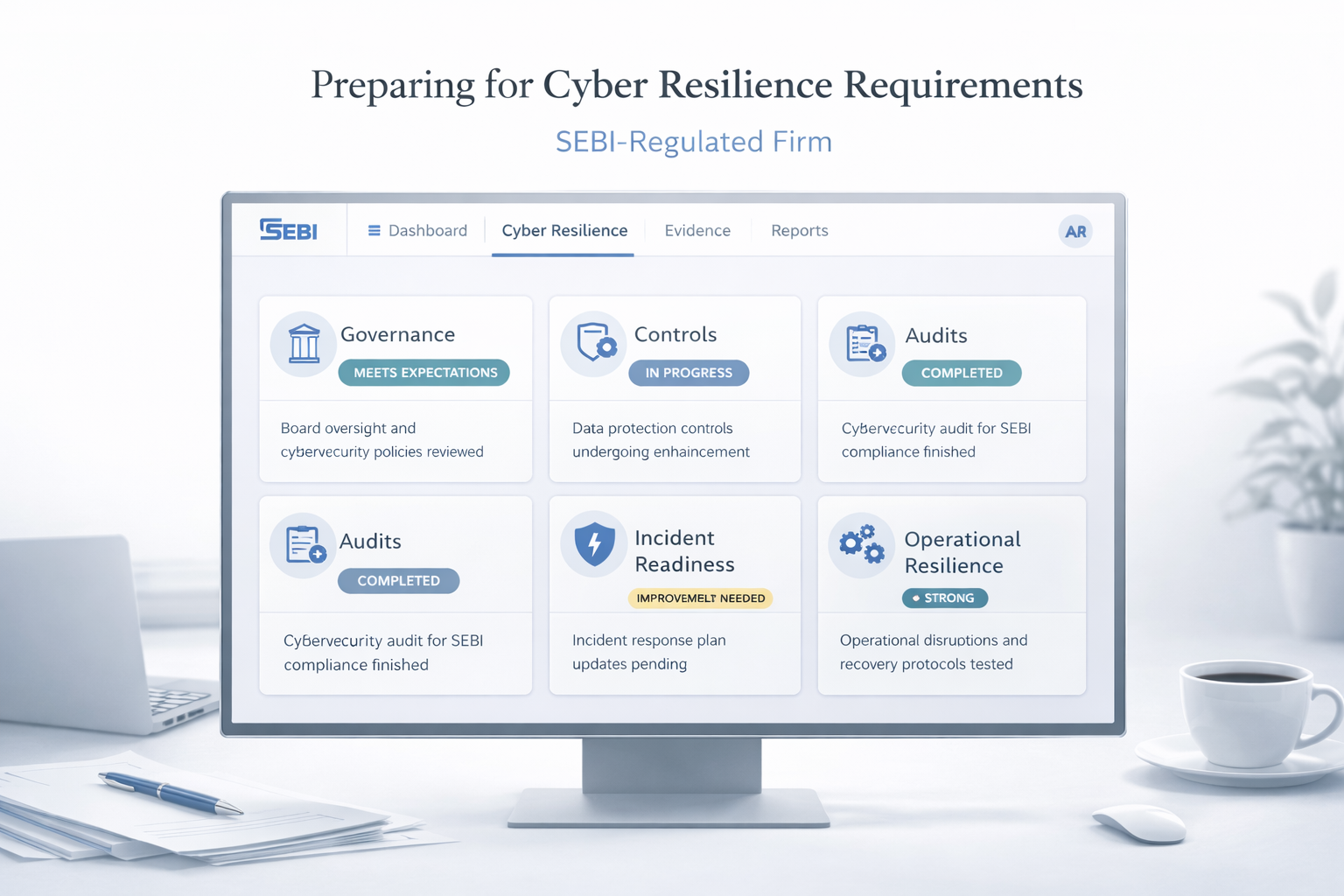
CSCRF changes the conversation because it makes cyber a management issue, not just a technical one. Once a regulator creates a formal resilience framework, senior stakeholders can no longer treat cyber as something the technology team “handles somewhere in the background.” Governance means the firm needs clearer internal ownership, clearer reporting lines, better escalation discipline, and more visible oversight. In practical terms, firms should prepare for cyber discussions to move closer to compliance, risk, internal control, and leadership review. This is the natural consequence of SEBI framing cyber resilience as a regulatory expectation across regulated entities.
The second theme is controls.
Many firms already have controls on paper. That is not the same thing as having a control environment that can withstand scrutiny. CSCRF pushes firms toward a more structured view of cyber controls, where the real question is not whether a policy exists, but whether the firm can show that key safeguards are actually designed, implemented, monitored, and updated over time. Later SEBI guidance and FAQs on CSCRF discuss areas such as security operations centres, threat intelligence, response and recovery, incident classification, DC-DR drills, and ISO 27001-related questions, which gives a good sense of how operational the framework becomes in practice.
For compliance teams, that matters because cyber controls are no longer just technical safeguards. They increasingly affect regulatory defensibility. If a firm says it has resilience, it should be able to show what controls support that claim.
The third theme is audits and evidence.
This is where many firms will feel the shift most sharply. Under older habits, cyber readiness could be discussed in broad language. A policy existed. A vendor was appointed. Some checks happened. But when a framework becomes more formal, vague comfort stops being enough. The firm has to think in terms of evidence. What was reviewed? What was tested? What was identified as weak? What was fixed? What is being tracked? Even the reporting formats SEBI later issued around CRiO-style reporting reflect this movement toward structured visibility and monitoring.
That means entities should prepare not just for cyber work, but for cyber recordkeeping. If a control was reviewed, there should be a record. If an issue was identified, there should be ownership. If remediation was completed, there should be evidence. This is where cyber starts looking a lot like any other serious compliance discipline.
The fourth theme is operational readiness.
This is the part firms should not underestimate. Cyber resilience is not only about preventing bad events. It is also about being ready to respond, recover, communicate, and continue operating in a controlled way. SEBI’s own materials and later FAQs point toward a framework that includes response and recovery expectations, incident handling, and resilience-oriented operational measures.
That matters because many firms still think of cyber maturity as preventive maturity. They focus on stopping incidents. That is necessary, but incomplete. Operational readiness asks harder questions. If something goes wrong, who is informed? Who decides severity? What gets documented? What must be escalated? How does the business continue? Where is the audit trail? Those are not purely technical questions. They sit at the intersection of compliance, risk, operations, and technology.
This is why CSCRF is changing the compliance conversation.
It forces regulated entities to stop treating cyber as an isolated function. It pushes firms to think in a more integrated way about governance, controls, audits, and operational readiness. It also creates a higher expectation of internal discipline. Not just awareness. Not just policy language. Not just outsourced reassurance. Actual structured preparedness.
For firms preparing in a sensible way, the best starting point is not panic. It is clarity.
First, identify who owns cyber governance internally and whether that ownership is real or merely assumed. Second, review whether your control environment is documented in a way that can be explained and defended. Third, check whether evidence of reviews, testing, remediation, and escalation is actually retrievable. Fourth, examine whether your incident and recovery processes are operational or only theoretical. Those are the right preparatory questions because they reflect the direction of the framework itself.
The deeper point is simple. CSCRF is not just a cyber circular. It is part of a wider regulatory shift toward demonstrable control. Firms that still run cyber through scattered policies, informal follow-up, or siloed ownership should take that seriously. The safer assumption going forward is that SEBI expects regulated entities to show not just that they care about cyber, but that they can govern it, operate it, review it, and evidence it properly.
That is why CSCRF matters beyond the technology team.
It is changing the compliance conversation because it is changing what preparedness now has to look like.
Explore related compliance hubs
Continue from this explainer into topic hubs that connect analysis with regulator updates and workflow context.
Related regulator archives
Continue into source-linked archives for regulators connected to this topic area.
Related regulatory updates
Source-linked updates that help place this article in the current regulatory workflow.
SEBI | Published 08 May 2026
Consultation Paper on Review and Rationalization of (Buy-Back of Securities) Regulations, 2018
NSE | Published 08 May 2026
Reversal Trade Cancellation Mechanism (RTCM) in Equity & Equity Derivatives Segment (Five trading days horizon)
NSE | Published 08 May 2026
Unique Client Code for Electronic Gold Receipts (EGRs) Segment
Content accountability
Prepared by CompliSense Editorial Desk (Regulatory Content Team).
This attribution reflects the preparation role used for CompliSense regulatory publishing.